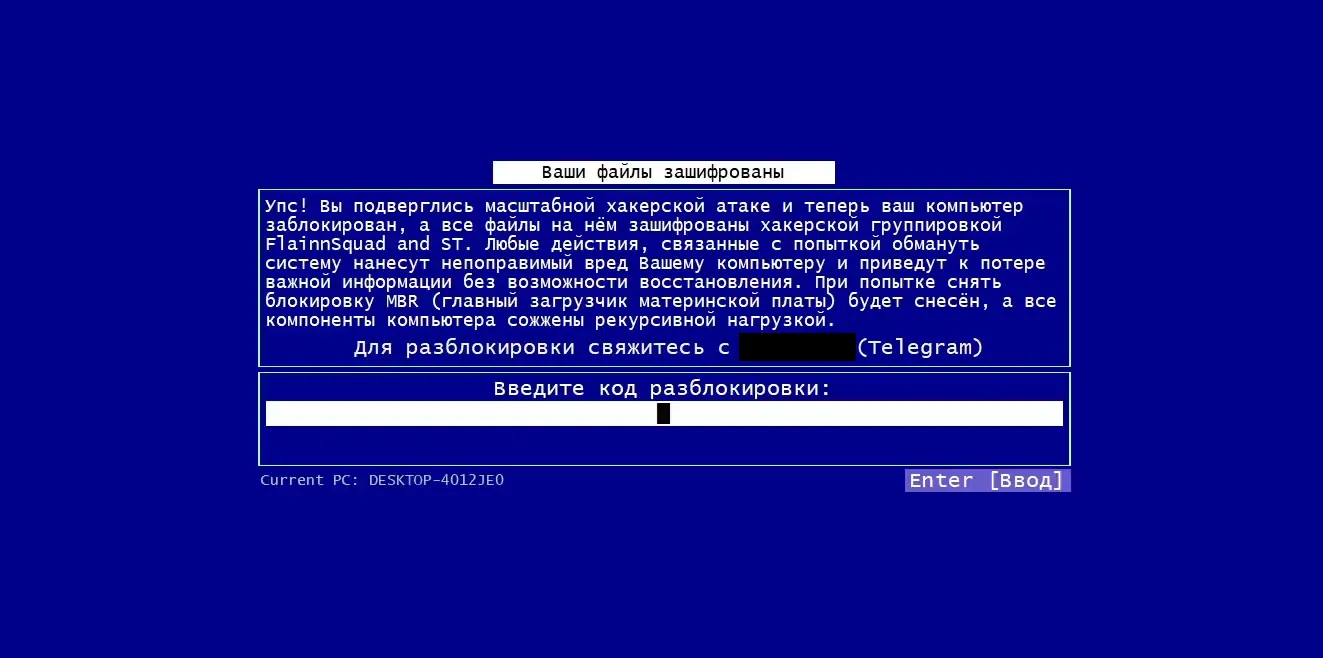
I found this “locker” when someone on Reddit recovered it from a Baldi’s Basics mod, It presents victims with a threatening screen demanding payment in TON coin, Telegram’s official cryptocurrency.
I wouldn’t normally write about this kind of malware since they are everywhere, but I decided to investigate this one deeper for some reason — and I’m very glad I did.
This is easily one of the worst ransomware samples I’ve ever looked at.
I examined the original links from the victim but found nothing suspicious, so I did a reverse image search on the ransom screen. This led me to discover a sample from an old any.run test, and from there, things got interesting.
First, this “ransomware” doesn’t actually encrypt anything, it’s just a fullscreen window that can be easily minimized or tabbed out of. The “encryption” is literally just a command it runs that hides files from showing up in explorer
attrib +h +s +r +i /D /S *Paying the ransom would simply unhide the files, and I doubt the malware even implements this functionality.
When I analyzed this sample, I was surprised to see anti-VM protections which turned out to be just a check against the computer’s manufacturer string, A quick DiE scan revealed that the malware was made in Visual Basic and also featured light obfuscation
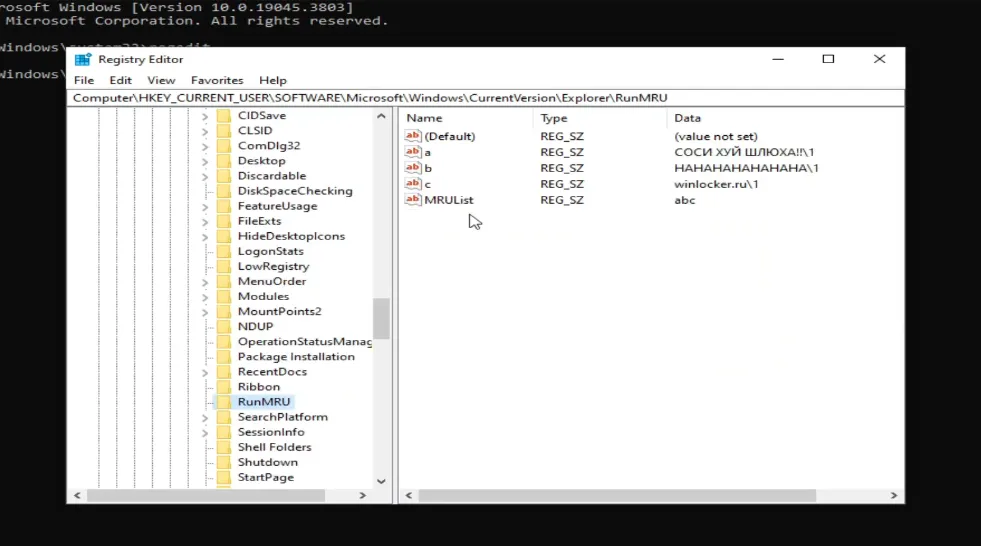
The malware overwrites the Winlogon Shell key in the registry to execute itself on startup and also inserts itself into the Microsoft Edge auto-updater registry key. It also writes to RunMRU with useless junk
But surely there’s worse batch script malware out there, right? Of course there is. What surprised me, however, is how many people were affected by this. From what I gathered, this malware primarily spread through itch.io games, and I found countless infected users.
I also discovered that this malware was leaked on GitHub at some point, which explains why there are so many variations of it